- Innovation For Future!
- +966 5010 39324
- +973 3512 8230
- info@cubicsolutions.org

Rising trend of online marketing in Saudi Arabia
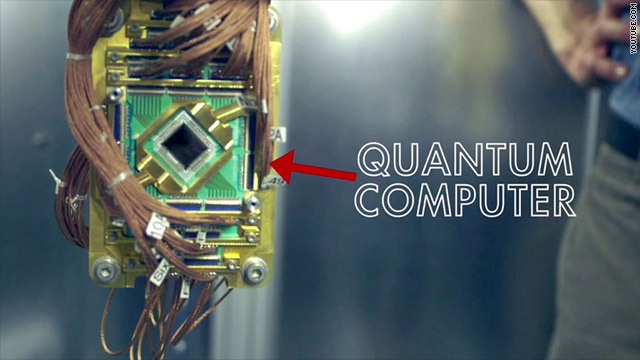
October 14, 2019Will Google’s Quantum computing Skynet 2.0 destroy Crypto
Quantum computers, initially theorized in 1982 by scientist Richard Feynman, is a new way of computing – one that allows mankind to be able to calculate what is not possible using today’s computing technologies and have secured a new era of computing.
Speculations have solely recently been translated into vital real-world advances on quantum computers with NASA, the CIA and Google. Currently computer scientists warn that machines can cripple existing cryptography strategies and destroy the technological foundations of bitcoin and other crypto currencies.
QUANTUM COMPUTING – A THREAT TO CRYPTO AND BLOCK-CHAIN
When it comes to extraordinary computational power, Quantum Computers are the prime suspects solving problems most traditional computers fail to do. The world’s most prominent problems, like global climate change, will only be overcome by machines like quantum computers.
Nevertheless, like all new technologies, it has the potential to present alternatives to obsolete alternative technologies. These technologies must be changed to survive and thrive, leaving as an alternative within the junk of one-hit Marvel technologies.
Considering blockchain and crypto, quantum computing is the obvious predator. Crypto and blockchain’s security comes from it’s enhanced encryption standards, but the power of quantum computing will surely knock it off the brick.
This is technically attainable for classical computers to interrupt through uneven cryptography that coins such as bitcoins use, using sheer brute force (running through all notable solutions). It will just take a terribly long time.
Quantum computers operate at a much faster speed than classical computers, and it is easier to defeat uneven cryptography. The 53-qubit quantum will breakthrough any of the 53 bit cryptography within seconds, meaning bitcoin’s 256 bit cryptography is vulnerable once google gets to scale its quantum computing to 256 qubits, one thing their own scientists say is going to be done by 2022.
GOOGLE OBTAINS “SKYNET” QUANTUM COMPUTERS FROM D-WAVE
Google and the National Aeronautics and Space Administration have currently set out to purchase a 512-qubit quantum computer SKYNET 2.0 from D-Wave. The computer is called “D-Wave Two” because it is the second generation of the system. The primary system was a 128-qubit computer, gen 2 is currently a 512-qubit computer.
This does not mean that the gen 2 system is just four times more powerful than the gen 1 system. Due to the character of the qubits, it is actually 384 times (2^384) more powerful compared to the gen 1 system.
In alternative words, it leaves the primary D-wave computer and computes at such a scale by an element that you cannot imagine it even in your human brain.
Google has been heavily funding in 3 major areas of research:
- Artificial Intelligence (machine learning, etc.)
- Quantum Computing
- Humanoid Robotics
When you mix these 3, you get one thing that’s beyond Skynet. You eventually produce an all-seeing AI intelligence that will connect all secrets and management to all monetary transactions.
With AI rapidly advancing human intelligence, and all the secrets with quantum computing being fully exposed to AI systems, it was entirely before the Google Super Intelligent System (or hence its name) of the time. The thing is, enslaves humanity and decides that we are no longer necessary for its survival.
CAN QUANTUM COMPUTING KILL CRYPTO
If quantum computing analysis continues at its current pace, it will have no downside to breaking the cryptography used by the blockchain and crypto. The economic system of crypto-currencies will become useless as it would be appropriate for hackers to steal your coins, commit fraud, and control the blockchain.
A major concern is that, quantum computing will easily break public key encoding. Quantum computing is projected to achieve this level of power by 2027.
In alternative terms, it would become very useless if today’s encoding standards and, by extension, blockchain security, do not develop new security technologies or encoding standards.
GULF NATIONS JOIN IN ON QUANTUM COMPUTING RESEARCH
Nations within the Gulf have launched a campaign towards quantum computing analysis through data acquisition teams to cultivate original data and ensure they are advancing the digital landscape.
The drive is set to enter universities in Saudi Arabia, Qatar and the United Arab Emirates (UAE), which have launched quantum computing analysis teams. While the worldwide quantum computing system continues in its infancy, the United States is reaching out to international tech giants to form early-stage partnerships.
Large-scale IT firms in the United States such as IBM, Google and Microsoft are investing in quantum computing in analytics. The UAE minister for AI recently partnered with Canadian company D-Wave to accommodate the region’s early quantum computers within the Future Museum in Dubai.
Last year, Dubai Electricity and Water Authority (Deva) proclaimed plans to working with Microsoft in developing a quantum-based business for its energy improvement where classical computers have serious limitations, to participate within Microsoft Creates primary organizations outside the United States. Quantum program.
POST-QUANTUM ENCRYPTION
Assuming that with many years of development, quantum computers reach the point where public-key cryptography is simply broken, should you bother and inspire a world where electronic transactions may not be secure?
Well, not exclusively. There are already many studies to direct quantum cryptography, such as lattice-based cryptography, multivariate cryptography or hash-based cryptography, all of which are strong candidates to gain our knowledge in an ultra-post-quantum world.
Of course, no one knows how long it will take to address potential weaknesses in post-quantum cryptography or perhaps if they will be sufficiently reliable to protect their transactions.
ENDING NOTE
Even though new cryptography strategies are introduced for future security, there is nothing to stop people exploiting quantum computing to show protected data using today’s cryptos. As an example, the National Security Agency or GCHQ can store interested emails and communications of interest, which they have developed as a part of their international surveillance.
It can be impossible to browse those nowadays, although in a very few years’ time, once quantum computers are out for deep-pocket intelligence agencies, the latter are able to sniff out all the conversations that we thought Used to be that they were non-absolute public, which could have some attention-grabbing results in the years of return.
![CTS-Horizontal-Logo[500px]](https://www.cubicsolutions.org/wp-content/uploads/2017/11/CTS-Horizontal-Logo500px.png)
